TechCrunch
TechCrunch
While most governments lean toward privacy-focused apps that use Bluetooth signals to create an anonymous profile of a person’s whereabouts, others, like Israel, use location and cell phone data to track the spread of the virus.
Israel-based private security firm NSO Group, known for making mobile hacking tools, is leading one of Israel’s contact-tracing efforts.
Security researcher Bob Diachenko discovered one of NSO’s contact-tracing systems on the internet, unprotected and without a password, for anyone to access. After he contacted the company, NSO pulled the unprotected database offline. Diachenko said he believes the database contains dummy data.
NSO told TechCrunch that the system was only for demonstrating its technology and denied it was exposed because of a security lapse. NSO is still waiting for the Israeli government’s approval to feed cell records into the system. But experts say the system should not have been open to begin with, and that centralized databases of citizens’ location data pose a security and privacy risk.
Codename ‘Fleming’
NSO began work on its contact-tracing system codenamed Fleming in March.
Fleming is designed to “pour” in confirmed coronavirus test data from the health authorities and phone location data from the cell networks to identify people who may have been exposed to a person with the virus. Anyone who came into close proximity to a person diagnosed with coronavirus would be notified.
The unprotected database was hosted on an Amazon Web Services server in Frankfurt, where the data protection regime is one of the strictest in the world.
It contained about six weeks of location data, spanning around March 10 to April 23. It also included specific dates, times and the location of a “target” — a term that NSO used in the database to describe people — that may have come into contact with a potentially infected person.
The data also included the duration of the encounter to help score the likelihood of a transmitted infection.
The login page for NSO’s Fleming is protected with a password. Its backend database was unprotected. (Image: TechCrunch)
“NSO Group has successfully developed ‘Fleming’, an innovative, unique and purely analytical system designed to respond to the coronavirus pandemic,” said Oren Ganz, a director at NSO Group. “Fleming has been designed for the benefit of government decision-makers, without compromising individual privacy. This system has been demonstrated worldwide with great transparency to media organizations, and approximately 100 individual countries,” he said.
TechCrunch was also given a demonstration of how the system works.
“This transparent demo, the same shown to individual countries and media organizations, was the one located on the open random server in question, and the very same demo observed today by TechCrunch. All other speculation about this overt, open system is not correct, and does not align with the basic fact this transparent demonstration has been seen by hundreds of people in media and government worldwide,” said Ganz.
John Scott-Railton, a senior researcher at the Citizen Lab, part of the Munk School at the University of Toronto, said that any database storing location data poses a privacy risk.
“Not securing a server would be an embarrassment for a school project,” said Scott-Railton. “For a billion-dollar company to not password protect a secretive project that hopes to handle location and health data suggest a quick and sloppy roll out.”
“NSO’s case is the precedent that proves the problem: rushed COVID-19 tracking efforts will imperil our privacy and online safety,” he said.
Israel’s two tracing systems
As global coronavirus infections began to spike in March, the Israeli government passed an emergency law giving its domestic security service Shin Bet “unprecedented access” to collect vast amounts of cell data from the phone companies to help identify possible infections.
By the end of March, Israeli defense minister Naftali Bennett said the government was working on a new contact tracing system, separate from the one used by Shin Bet.
It was later revealed that NSO was building the second contact-tracing system.
Tehilla Shwartz Altshuler, a privacy expert and a senior fellow at the Israel Democracy Institute, told TechCrunch that she too was given a demonstration of Fleming over a Zoom call in the early days of the outbreak.
Without the authority to obtain cell records, NSO told her that it used location data gathered from advertising platforms, or so-called data brokers. Israeli media also reported that NSO used advertising data for “training” the system.
Data brokers amass and sell vast troves of location data collected from the apps installed on millions of phones. The apps that track your movements and whereabouts are often also selling those locations to data brokers, which then resell the data to advertisers to serve more targeted ads.
NSO denied it used location data from a data broker for its Fleming demo.
“The Fleming demo is not based on real and genuine data,” said Ganz. “The demo is rather an illustration of public obfuscated data. It does not contain any personal identifying information of any sort.”
Since governments began to outline their plans for contact-tracing systems, experts warned that location data is not accurate and can lead to both false positives and false negatives. Currently, NSO’s system appears to rely on this data for its core functions.
“This kind of location data will not get you a reliable measure of whether two people came into close contact,” said Scott-Railton.
NSO’s connection to the Middle East
Israel is not the only government interested in Fleming. Bloomberg reported in March that a dozen nations were allegedly testing NSO’s contact-tracing technology.
A review of the unprotected database showed large amounts of location data points in Israel, but also Rwanda, Saudi Arabia and the United Arab Emirates.
Spokespeople for the Saudi, Rwandan and Emirati consulates in New York did not respond to our emails. NSO did not answer our questions about its relationship — if any — with these governments.
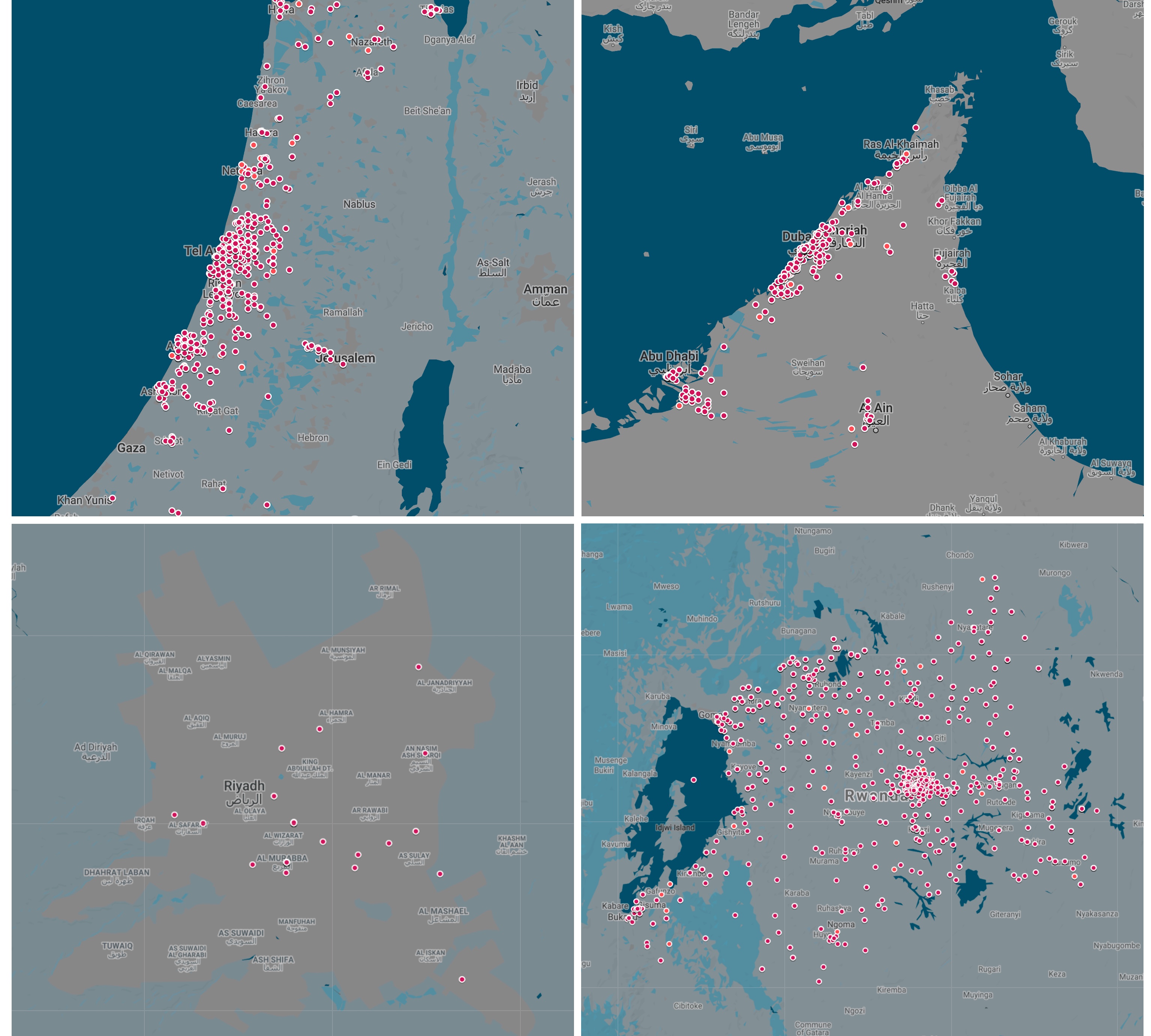
A map showing a sample of about 20,000 location data points across Israel (top-left); Abu Dhabi and Dubai, United Arab Emirates (top-right); Riyadh, Saudi Arabia (bottom-left) and Rwanda (bottom-right). (Image: TechCrunch)
Saudi Arabia is a known customer of NSO Group. United Nations experts have called for an investigation into allegations that the Saudi government used NSO’s Pegasus spyware to hack into the phone of Amazon chief executive Jeff Bezos. NSO has denied the claims.
NSO is also embroiled in a legal battle with Facebook-owned WhatsApp for allegedly building a hacking tool designed to be delivered over WhatsApp, which was used to hack into the cell phones of 1,400 users, including government officials, journalists and human rights activists, using AWS servers based in the U.S. and Frankfurt. NSO also rebuffed the claims.
Privacy concerns
Experts have expressed concerns over the use of centralized data, fearing that it could become a target for hackers.
Most countries are favoring decentralized efforts, like the joint project between Apple and Google, which uses anonymized Bluetooth signals picked up from phones in near proximity, instead of collecting cell location data into a single database. Bluetooth contact tracing has won the support of academics and security researchers over location-based contact-tracing efforts, which they say would enable large-scale surveillance.
Shwartz Altshuler told TechCrunch that location-based contact tracing is a “huge infringement” of privacy.
“It means that you can’t have any secrets,” she said. “You can’t have any meetings if you’re a journalist, and you can’t go to places where people want to know where you are.”
Favoring their own contact-tracing efforts, Apple and Google have already banned governments building contact-tracing apps utilizing their joint API from using location tracking, fearing that data stored on a centralized server could be breached.
Just this week, the U.S. and U.K. governments warned that nation-state hackers are targeting organizations involved in the coronavirus response.
Alan Woodward, a professor at the University of Surrey, said location data makes it “possible to build social graphs and to begin identifying who met who, when and where.”
“Even if it is just trial data, it’s still sensitive if it’s real people,” he said.
]]>



